Cross-chain bridges are the lifelines of blockchain interoperability, powering everything from DeFi swaps to NFT transfers across networks. But beneath their seamless user experience lies a web of trust assumptions that can make or break their security. As the market continues to evolve and bridge protocols handle ever-larger volumes, understanding how these trust models work - and where they fall short - is essential for anyone serious about cross-chain bridge security risks.
Why Trust Models Matter: The Hidden Backbone of Cross-Chain Bridges
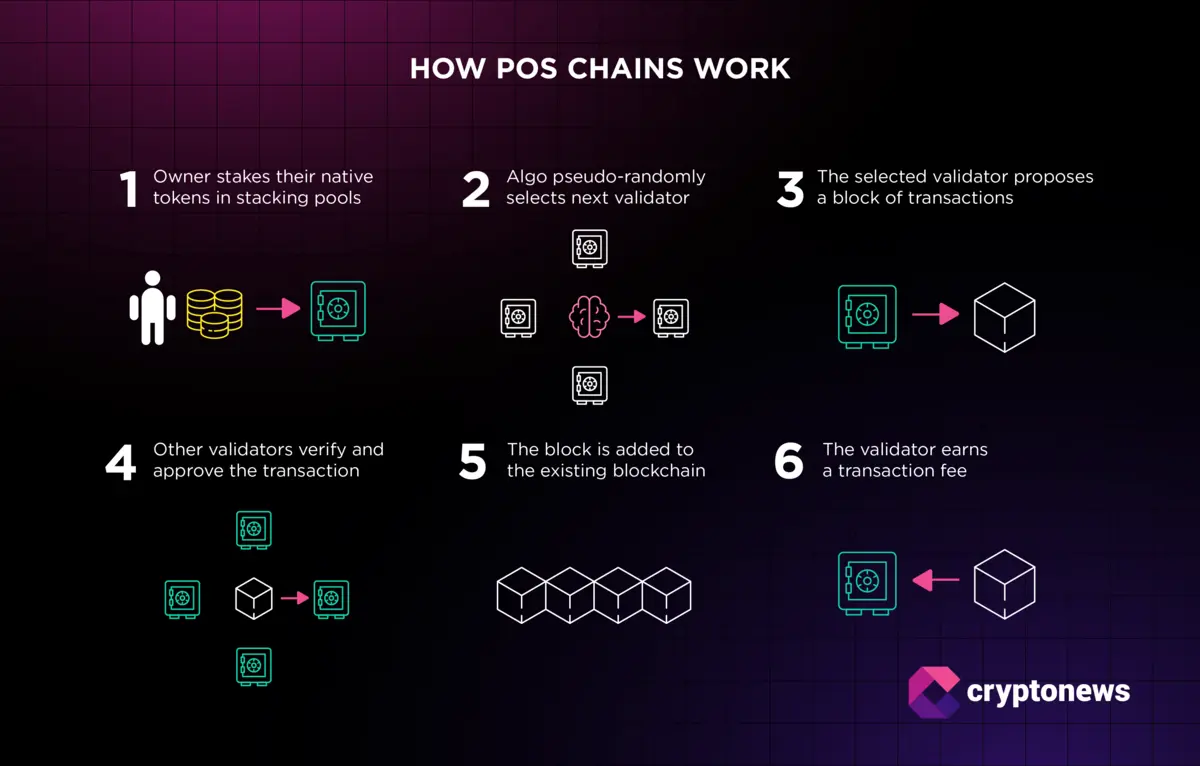
Every cross-chain bridge relies on a set of validators, signers, or committees to confirm and relay transactions between blockchains. This underlying trust model is not just a technical detail; it’s the foundation that determines the protocol’s resilience against attacks.
Let’s get real: when you move assets across chains, you’re putting faith in the bridge’s ability to keep those assets safe from hackers and insider threats. The two most common architectures, multisignature (multisig) wallets and multi-party computation (MPC): each come with their own strengths, but also introduce unique vulnerabilities that have been ruthlessly exploited in recent years.
Multisig Vulnerabilities: When Shared Control Becomes a Single Point of Failure
Multisig wallets sound robust in theory. Instead of one private key holding all the power, transactions require approval from a group, say 3 out of 5 or 5 out of 9 validators. But here’s where things get dicey:
- Low Thresholds = High Risk: If the number of required signatures is too low relative to the total validator set, attackers only need to compromise a handful of keys. The infamous Ronin Bridge hack is a textbook example, by nabbing just five out of nine keys, attackers made off with over $600 million.
- Poor Validator Diversity: When validators are controlled by related entities or lack geographic/administrative diversity, collusion becomes a real threat. All it takes is some backroom dealing or social engineering for an attacker to gain majority control.
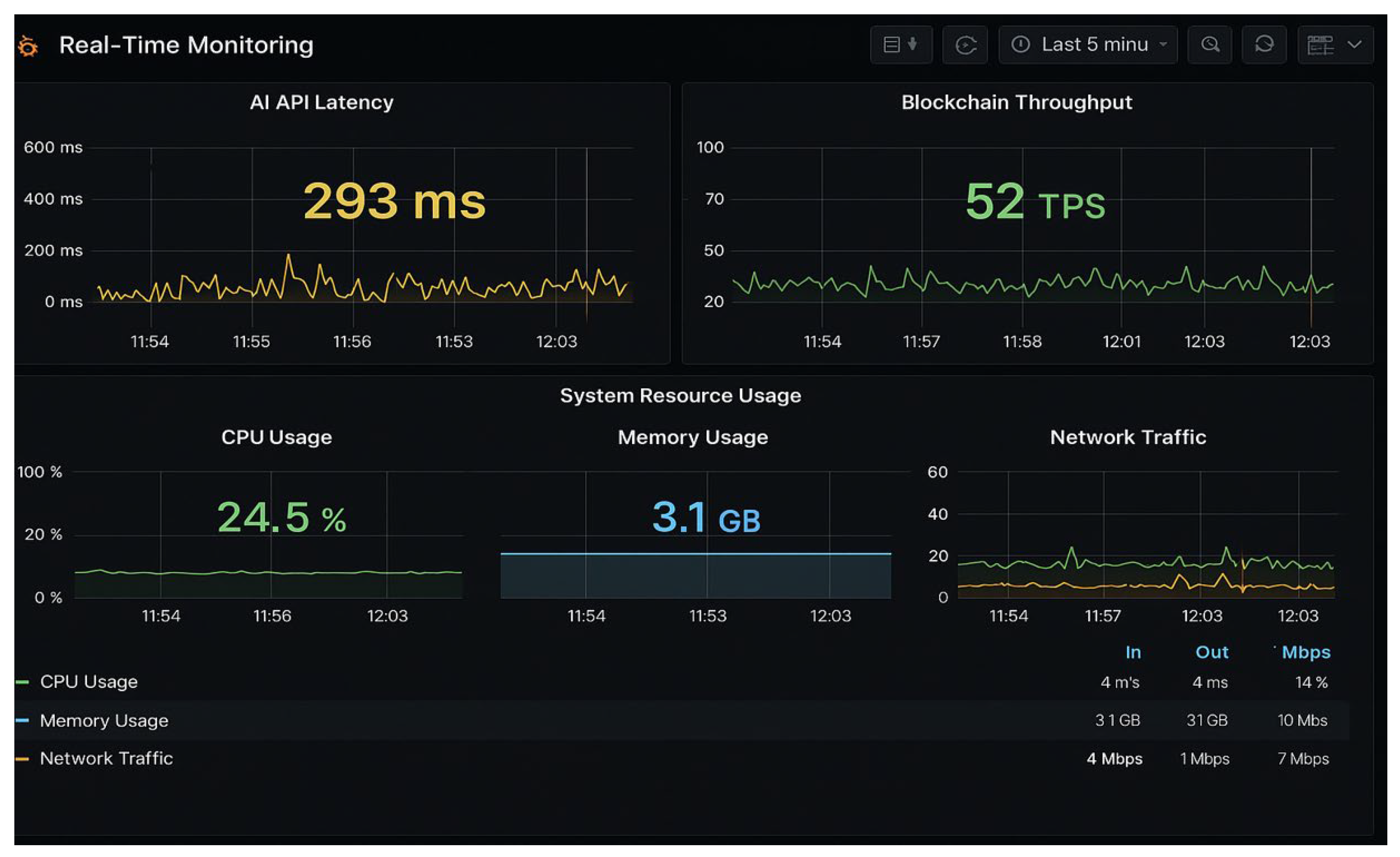
- Lack of Real-Time Monitoring: Without active anomaly detection and emergency halts, multisig bridges can’t react fast enough when something goes wrong. By the time anyone notices irregular activity, funds could be long gone.
The reality? Multisig setups are only as strong as their weakest link, and history shows that weak links are all too common in today’s cross-chain ecosystem.
MPC: Cutting-Edge Tech With Its Own Set of Landmines
MPC schemes promise to remove single points of failure by splitting private key control among multiple parties who never see each other’s shares. In theory, this should make bridges safer, but there’s no such thing as perfect security:
- Threshold Dilemmas: Just like multisigs, if signature thresholds are set too low or if parties aren’t truly independent, attackers can still coordinate an exploit.
- Side-Channel Attacks: Even if key shares aren’t directly exposed, clever adversaries might extract sensitive info through timing analysis or network leaks during MPC computations.
- MPC Coordinator Risks: Many implementations depend on a coordinator service to orchestrate key generation and signing sessions. If this coordinator fails, or worse, gets compromised, the entire system can grind to a halt or be hijacked outright.
The bottom line? While MPC raises the bar for would-be attackers compared to basic multisigs, it introduces new attack surfaces that require constant vigilance and world-class operational security.
The Growing Stakes: Why Bridge Security Can’t Be an Afterthought
The numbers don’t lie, bridge protocols collectively lost over $1, 2 billion in recent years due to compromised trust assumptions (see Chainlink and Turnkey reports). Attackers aren’t just going after smart contract bugs anymore; they’re targeting governance structures and validator coordination itself.
If you’re building, or using, a cross-chain protocol today, you need more than just code audits. You need ongoing risk scanning tools, robust validator decentralization strategies, and real-time monitoring capabilities baked into your stack from day one.
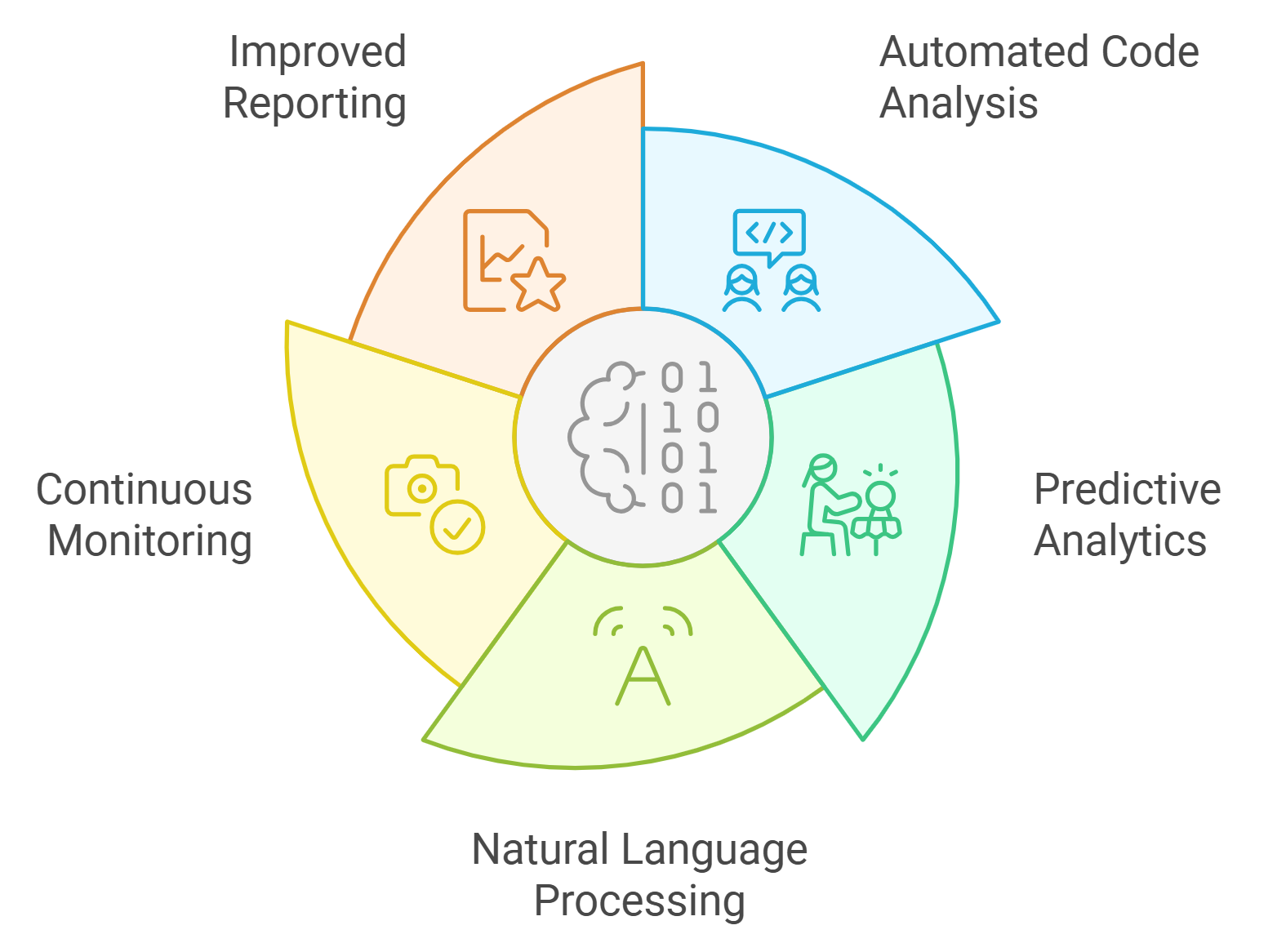
Smart contract audits are only the first step. The real challenge is operational: how do you continuously monitor, update, and stress-test your bridge’s trust assumptions as the ecosystem evolves? Attackers adapt quickly, and so must defenders. This means not just reacting to incidents, but proactively identifying where your multisig or MPC setup could be gamed, before it happens.
Best Practices for Cross-Chain Bridge Security
- Secure Key Management: Use hardware security modules (HSMs) and advanced multi-party computation (MPC) protocols to protect private keys. Solutions like Fireblocks and Copper ClearLoop offer institutional-grade key management for bridges.

- Live Risk Scanning & Monitoring: Implement real-time monitoring tools such as Chainalysis or HAL to detect suspicious activities, anomalies, and potential exploits as they happen.
- Regular Protocol Audits: Partner with reputable security firms like Trail of Bits, ConsenSys Diligence, or CertiK for comprehensive smart contract and protocol audits to uncover vulnerabilities before attackers do.
Let’s break down what separates a resilient bridge from a sitting duck:
- Validator Diversity: Spread your validator set across different legal jurisdictions, organizations, and infrastructure providers. This isn’t just about decentralization for its own sake, it’s about making collusion or mass compromise exponentially harder.
- Key Management Hygiene: Use hardware security modules (HSMs) or battle-tested MPC implementations for all key operations. Rotate keys regularly and keep strict access controls in place.
- Continuous Risk Assessment: Integrate real-time anomaly detection that can flag suspicious transactions and trigger emergency shutdowns if needed. Don’t wait for a post-mortem to find out where you went wrong.
Staying Ahead of Cross-Chain Bridge Exploits
The unfortunate truth is that cross-chain bridges will always be lucrative targets for attackers. As more value flows across chains, the incentives only grow. But that doesn’t mean users and builders are powerless, far from it.
If you’re a developer or protocol operator, prioritize transparency around your trust model. Publish detailed documentation on how validator sets are chosen and rotated. Share results from recent audits and bug bounties. Make it easy for users to understand the risks they’re taking, and show them what you’re doing to minimize those risks every day.
For users: Don’t just chase high yields or flashy new features without due diligence. Look for bridges that have been independently audited multiple times, maintain active monitoring dashboards, and are transparent about their validator structure and incident response plans. If something feels opaque or centralized, trust your gut and look elsewhere.
The future of blockchain interoperability depends on getting these trust models right. As we saw with the Multichain exploit and others like it, even advanced architectures can collapse if operational security lags behind technical innovation. The projects that thrive will be those who treat trust minimization as a living process, not a box checked at launch.
If you want to dive deeper into the nuances of cross-chain trust models (and actionable ways to harden your protocol), check out our comprehensive guide at this resource.





No comments yet. Be the first to share your thoughts!