Cross-chain bridges are the connective tissue of decentralized finance, enabling assets and data to flow seamlessly between disparate blockchains. But as these bridges scale to support billions in value, their underlying security assumptions come under intense scrutiny. The reality is stark: centralized validators remain one of the most acute risks to cross-chain bridge security, routinely exposing protocols to catastrophic, multi-billion dollar exploits.

Why Centralized Validators Are a Critical Weakness
The architecture of many high-profile bridges relies on a small set of validators or a multi-signature wallet controlled by a handful of entities. This setup dramatically simplifies the attack surface for adversaries. If an attacker can compromise just enough validator keys, whether through phishing, malware, social engineering, or insider collusion, they gain effective control over the bridge’s funds.
This isn’t just theoretical. The Ronin Bridge hack is now infamous for its simplicity and scale: attackers obtained five out of nine validator keys and siphoned off $625 million in assets. In the case of Harmony’s Horizon Bridge, only two out of five multisig signers needed to be compromised for attackers to drain $100 million (source). These events underscore how centralization transforms sophisticated cryptographic systems into low-hanging fruit for attackers.
Anatomy of Multi-Billion Dollar Bridge Exploits
The majority of major DeFi bridge hacks over the past two years have stemmed from validator centralization:
Major Cross-Chain Bridge Hacks from Validator Compromise
- Ronin Bridge Hack (March 2022): Attackers compromised five of nine validator keys on the Ronin Network—used by Axie Infinity—enabling unauthorized withdrawals totaling approximately $625 million. This remains one of the largest crypto thefts to date, highlighting the dangers of centralized validator control.

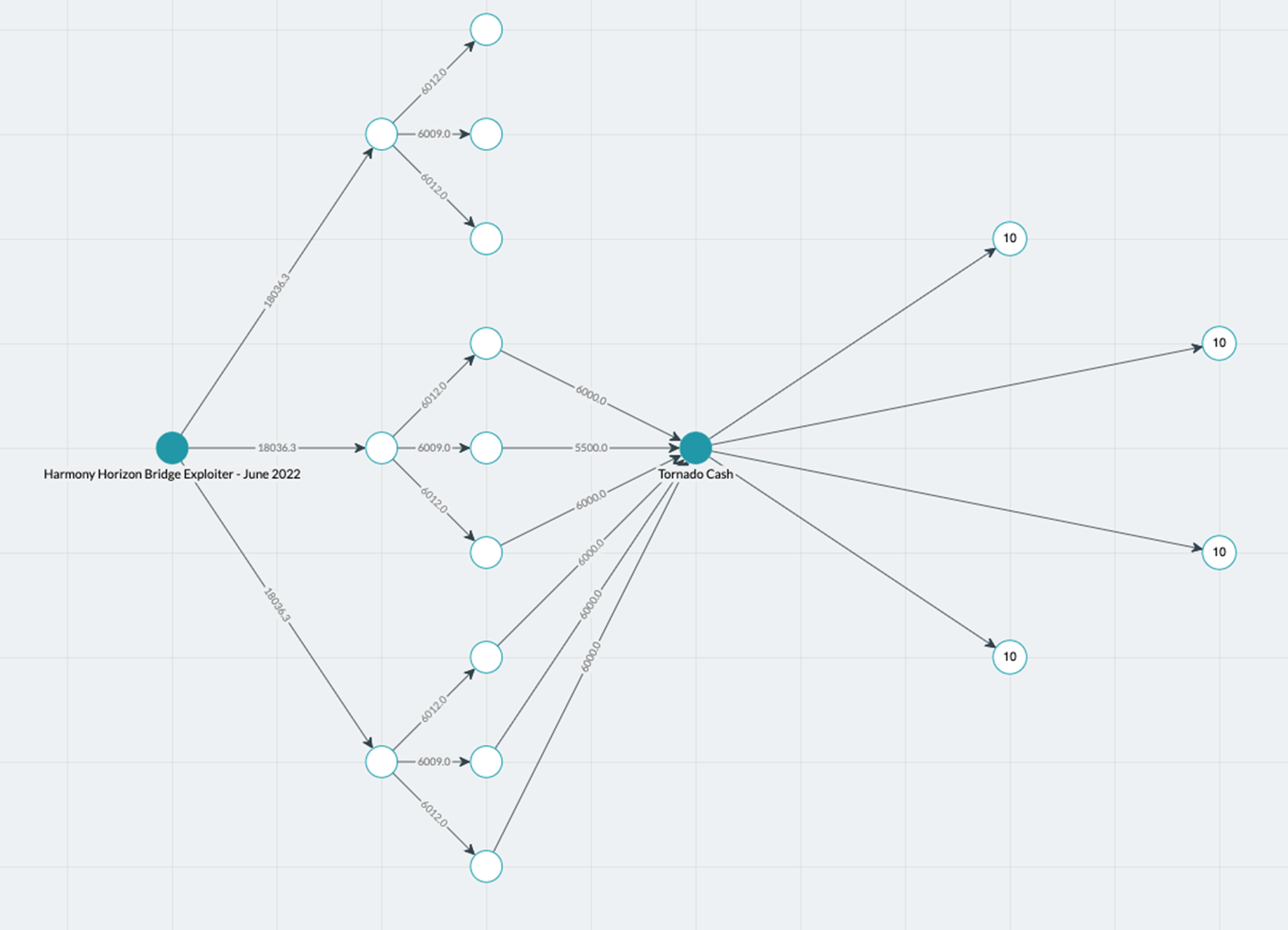
- Harmony Horizon Bridge Exploit (June 2022): The Harmony Horizon bridge relied on a 2-of-5 multisig validator setup. Attackers gained access to two validator keys, allowing them to approve malicious transactions and steal around $100 million in digital assets.
- Wormhole Bridge Attack (February 2022): Exploiting a vulnerability in the bridge's guardian nodes, an attacker bypassed signature verification and minted 120,000 Wrapped Ether (wETH) on Solana without depositing ETH on Ethereum, resulting in a loss of approximately $325 million.

The Wormhole exploit further illustrates this pattern. Here, vulnerabilities in guardian nodes, a form of validator, enabled attackers to bypass signature verification and mint 120,000 wETH on Solana without depositing any ETH on Ethereum. The result? A loss tallying $325 million (reference).
As highlighted by security researchers at Chainlink and Presto Labs, centralized validation not only increases risk but also undermines user trust in cross-chain infrastructure (see more). Attackers are incentivized to focus their efforts on these single points of failure where the reward-to-effort ratio is highest.
Mitigation Strategies: Moving Toward Trustless Validation
The industry’s response is clear: decentralize or die. Solutions range from expanding validator sets, making it exponentially harder for any single entity or coalition to seize control, to adopting trustless designs like zero-knowledge proof-based bridges (e. g. , zkBridge). Enhanced key management practices are non-negotiable; hardware security modules (HSMs), regular key rotation, and multi-factor authentication must be standard operating procedure for any serious protocol.
Real-time monitoring solutions such as XChainWatcher are emerging as critical tools for detecting suspicious activity before it escalates into full-blown exploits (source). However, technology alone isn’t enough without disciplined operational security and transparent governance frameworks.
Bridge operators and DeFi builders must recognize that decentralized validation is not a luxury, it's an existential requirement for the future of cross-chain finance. The alternative is a perpetual cycle of high-profile hacks, shaken user confidence, and regulatory scrutiny that threatens the entire ecosystem’s legitimacy.
Best Practices for Cross-Chain Bridge Security
Security is a moving target. As attackers evolve, so must defense strategies. The most resilient bridges in 2025 are those that combine multiple layers of protection, transparency, and continuous improvement. Here are the core pillars every bridge should implement:
1. Diverse Validator Sets: Expand the number and diversity of validators to dilute risk concentration. Incentivize participation from independent entities, not just protocol insiders.
2. Automated Key Rotation and Secure Storage: Employ HSMs, automate key rotation schedules, and enforce strict access controls as standard protocol hygiene.
3. On-Chain Transparency and Auditing: Make validator actions publicly auditable on-chain; introduce slashing penalties for misbehavior or downtime.
4. Real-Time Risk Scanning: Integrate tools that provide continuous monitoring and instant alerts for anomalous transactions or validator behavior.
5. Trustless Design Adoption: Move toward cryptographic validation (e. g. , zk-proofs) that minimizes reliance on any single party or group.
The harsh reality is that every bridge is a target. Attackers only need to succeed once, defenders must succeed every time. By implementing these best practices, protocols can significantly reduce their exposure while signaling to users and partners that security is non-negotiable.
The Road Ahead: Balancing Innovation with Discipline
The explosion in total value locked (TVL) across bridges has made them irresistible targets for sophisticated adversaries, and there’s no sign this trend will slow down as DeFi matures. Security teams must stay vigilant, leveraging both technical innovation and operational rigor to stay ahead of attackers.
If you’re building or using cross-chain infrastructure today, ask yourself: Would you trust your entire portfolio to a handful of validators? If not, demand better architecture, or risk being next in line for the headlines.
The industry’s most robust protocols are those that treat security as an ongoing process rather than a one-time checkbox exercise. Regular audits, community-driven governance improvements, bug bounty programs, and transparent incident response plans all play vital roles in hardening defenses against evolving threats.
If there’s one lesson from the past two years’ multi-billion dollar exploits, it’s this: Centralization breeds fragility. The path forward requires discipline, both technical and operational, to ensure cross-chain bridges become resilient pillars rather than weak links in the DeFi ecosystem.





No comments yet. Be the first to share your thoughts!