Cross-chain bridges power the multi-chain future of blockchain, yet they harbor a subtle threat: validator collusion risks that audits often overlook. In protocols like Wormhole and LayerZero, validators or their equivalents hold the keys to consensus, and if enough collude, bridges crumble. Recent exploits underscore this, with Wormhole's $320 million breach exposing flaws beyond code vulnerabilities. Developers and users must scrutinize these trust assumptions, as reputation alone fails against coordinated malice.
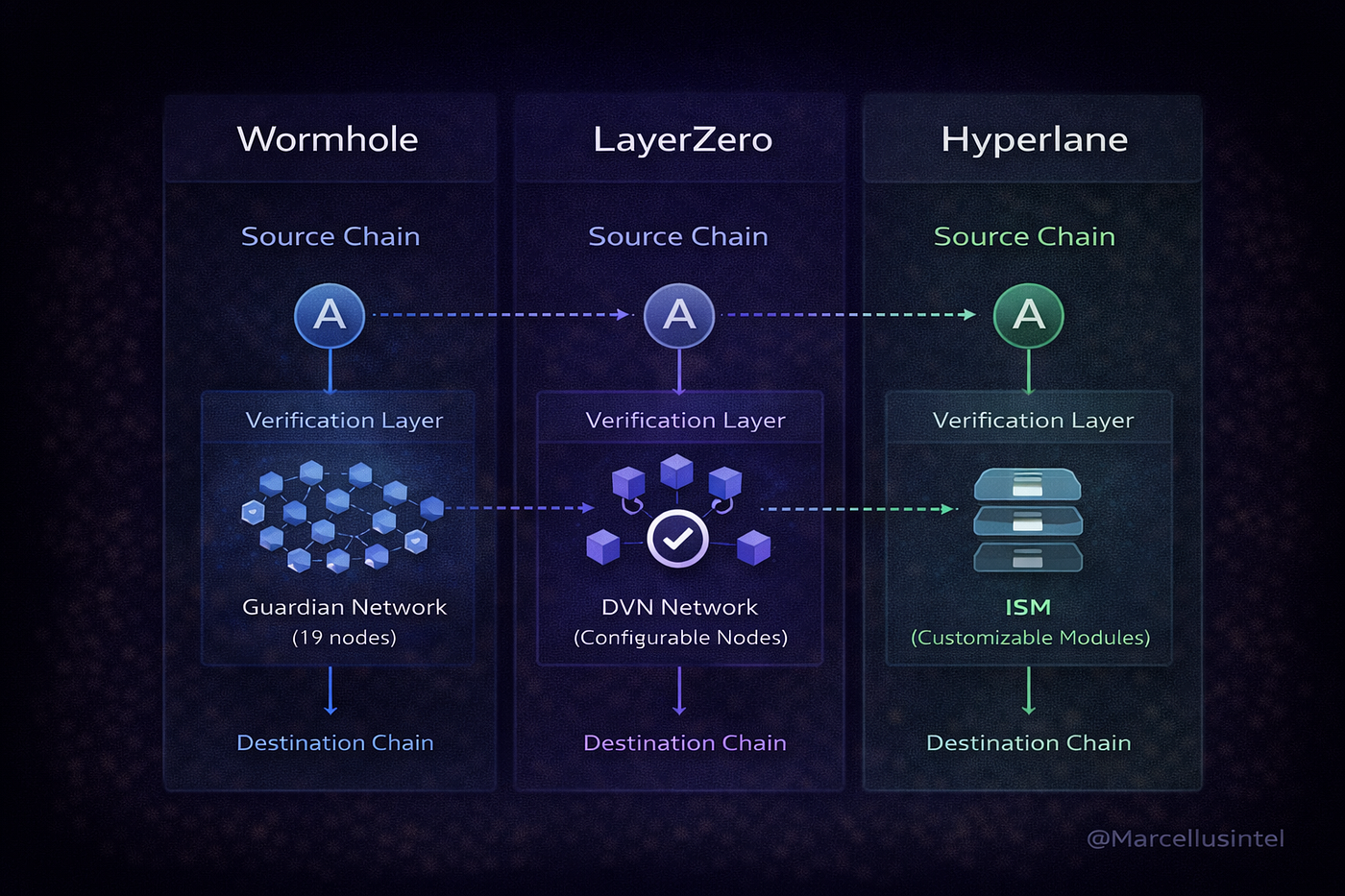
Bridges aggregate value across ecosystems, but their security hinges on decentralized verification. Wormhole's guardians and LayerZero's oracles-relayers model aim for robustness, yet both invite cross-chain messaging exploits through insider threats. Bridge security audits reveal code soundness, but human factors persist, demanding vigilant scanning.
Wormhole's Guardian Consensus: A Double-Edged Sword
Wormhole deploys a permissioned set of 19 validators, dubbed guardians, drawn from professional proof-of-stake operators. Actions require two-thirds approval, meaning 13 colluders could approve fraudulent messages. No slashing enforces honesty; instead, the protocol banks on reputational damage. This setup shone post its February 2022 exploit, where a signature verification bug let attackers mint 120,000 ETH worth $320 million, not collusion but a stark reminder of single points of failure.
Systemic risk amplifies when bridges fail, as Wormhole and Nomad hacks proved, per ChainScore Labs.
Guardian diversity mitigates some risks, yet centralization critiques linger. Professional validators prioritize uptime over aggression, but economic incentives could align for collusion during market stress. Top vulnerabilities in blockchain bridges often trace to such trust models, urging continuous bridge security audits.
LayerZero's Oracle-Relayer Split: Innovation or Illusion?
LayerZero sidesteps pure validator reliance by decoupling oracles and relayers. Oracles fetch blockchain states; relayers deliver messages. Compromise demands both colluding, raising the bar versus Wormhole's threshold. This modular design theoretically bolsters resilience against LayerZero vulnerabilities, yet independence isn't guaranteed. If operators overlap or share incentives, collusion thresholds drop.
The whitepaper touts this as trust-minimized, but real-world deployment tests it. No slashing here either, echoing Wormhole's reputational reliance. Audits like ChainSecurity's on Wormhole-LayerZero migration affirm code quality, yet warn of procedural adherence. In practice, validator collusion cross-chain remains a vector, especially as TVL grows.
Wormhole vs. LayerZero: Validator Collusion Risks Comparison
| Protocol | Validators Count | Collusion Threshold | Slashing Mechanism | Key Audit Findings |
|---|---|---|---|---|
| Wormhole | 19 | 13/19 (2/3 consensus) | None ❌ | Signature verification vulnerability (Feb 2022, 120,000 ETH loss) ⚠️ ChainSecurity audit: High security for LayerZero Migration Library ✅ |
| LayerZero | Decentralized (Oracles + Relayers) | Oracle + Relayer collusion required | Not specified | Architecture theoretically reduces collusion risk ⚠️ Concerns over entity independence persist ⚠️ |
Unpacking Historical Exploits and Audit Insights
Wormhole's breach stemmed from improper message validation, enabling unauthorized mints. Though not collusion-driven, it illuminated guardian verification gaps. Broader data paints a grim picture: 69% of 2022 crypto thefts linked to bridges, $1.4 billion gone, per CNBC via Quantum Canary. Ronin and Nomad echoed key compromises, fueling Wormhole risks debates.
Audits probe code but struggle with collusion simulations. Chainlink outlines seven key vulnerabilities, including validator theft or coordination. arXiv research notes even audited bridges fall, demanding anomaly detection. For Wormhole, post-exploit upgrades fortified signatures, yet the 13-guardian threshold endures. LayerZero's model, while clever, invites oracle-relayer cartel fears if decentralized enough.
Audit checklists for cross-chain messaging emphasize multi-party computation and economic penalties, absent in these protocols. Developers scanning for cross-chain messaging exploits should prioritize collusion stress tests, blending static analysis with game theory models. Reputation suffices in bull markets; bears test true mettle.
Game theory models reveal that rational actors might collude if rewards outweigh reputational hits, especially in opaque networks. Wormhole's guardians, while diverse, cluster around a few staking giants, shrinking the effective collusion pool. LayerZero's split raises similar flags: if a single entity controls both oracle and relayer endpoints, safeguards evaporate. Bridge security audits catch syntax slips but rarely model adversarial cartels.
Scanning Tools: Beyond Static Audits
Enter dynamic risk scanners tailored for cross-chain messaging exploits. Platforms like Cross-Chain Messaging Risk Scanners deploy real-time monitors tracking guardian uptime, message quorum anomalies, and off-chain validator correlations. For Wormhole, scans flag if 13 and guardians share IP ranges or voting patterns deviating from historical norms. LayerZero endpoints get probed for oracle-relayer overlap via endpoint tracing. These tools simulate collusion thresholds, outputting risk scores that evolve with network changes.
Such checklists operationalize vigilance. Developers integrate them pre-deployment, while users query TVL-adjusted exposure. Historical data from arXiv studies shows audited bridges still fall 20% more often to runtime anomalies than code bugs, underscoring proactive scanning's edge. Coinchange reports highlight how validator theft or coordination tops exploit vectors, often masked as legitimate consensus.
Collusion isn't just theoretical; it's the quiet multiplier in bridge failures, per Chainlink's vulnerability breakdown.
LayerZero's innovation shines in theory, but deployment metrics matter. Early adopters report relayer centralization in high-volume lanes, inviting targeted bribes. Wormhole countered its exploit with guardian rotations and enhanced VAA verification, yet the core threshold persists. Both protocols eye slashing via tokenomics upgrades, but implementation lags economic alignment.
Mitigations That Stick: From Reputation to Economics
True resilience demands layered defenses. First, expand validator sets beyond 19 for Wormhole-like setups, diluting collusion odds geometrically. Second, enforce verifiable randomness in guardian selection, thwarting predictable targeting. LayerZero could mandate decentralized relayer markets, audited for bid collusion. Economic penalties top the list: stake-linked slashing, as in Cosmos, deters defection. Yet slashing alone falters without fast finality; bridges need hybrid models blending MPC with threshold signatures.
Cross-chain protocols thrive on interoperability, but security lags breed hesitation. DeFi TVL funnels to audited yet unproven bridges, amplifying systemic blasts. Ronin's validator compromise stole $600 million; Wormhole's near-miss echoed it. Forward-thinking teams embed collusion simulators in CI/CD pipelines, stress-testing under bearish incentives. Users, arm protocols with on-chain bounties for anomaly reports, turning vigilance into value accrual.
Pragmatism rules: no bridge is unhackable, but informed scrutiny narrows the blast radius. Platforms scanning Wormhole risks and LayerZero vulnerabilities deliver dashboards fusing audit intel with live telemetry. Developers, prioritize these in your stack; protocols, evolve beyond reputation. The multi-chain era demands it, as collusion lurks in every quorum. Diversify bridges, monitor relentlessly, and hedge with insurance wrappers. In this arena, foresight isn't optional, it's the ultimate yield generator.
Practical risk assessment for cross-chain bridges





No comments yet. Be the first to share your thoughts!